Trusted by
The problem with existing trust service architectures
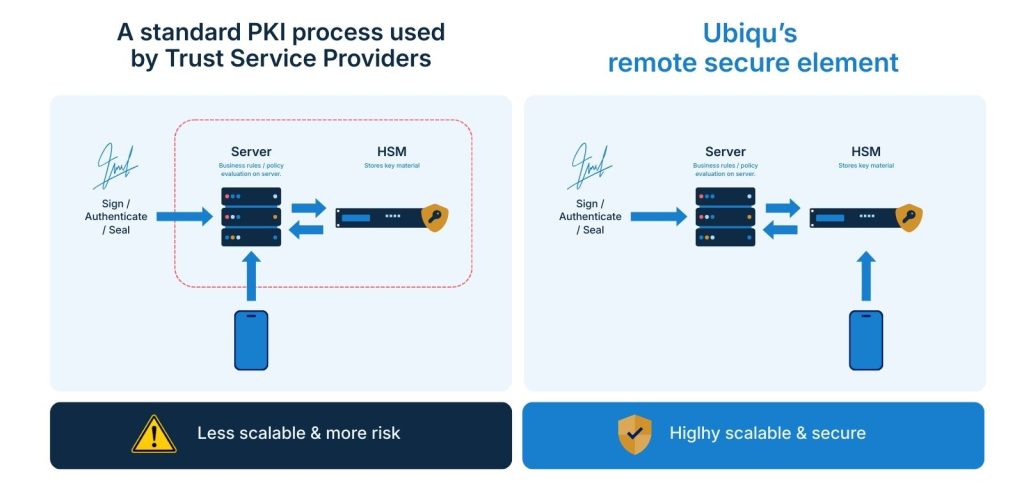
Many digital wallet and trust solutions are built on heavy, layered technology stacks that have grown over time to meet security and regulatory demands. The result is infrastructure that is expensive to run, difficult to oversee, and dependent on multiple systems and vendors. That complexity increases operational burden and expands the potential attack surface, making the overall setup harder to control and, in practice, more exposed to risk.
Most wallets and trust services today rely on architectures that are difficult to operate, scale, and certify. While cryptographic keys are typically stored in secure hardware, the decisions about when and how those keys may be used are handled outside of that environment, across application logic, orchestration layers, or custom-built systems. This separation makes compliance with eIDAS 2.0 frameworks such as WSCA and QSCD more complex, as the security boundary is fragmented and harder to assess and certify. It also increases operational overhead, since organisations must build and maintain additional layers for policy enforcement, approval flows, and integration. As usage grows, these architectures do not scale efficiently, because expanding capacity requires scaling the entire surrounding infrastructure rather than just the secure core. The result is either rigid, closed platforms that limit flexibility, or highly customised environments that are costly to run and difficult to maintain, even when they technically meet compliance requirements.
What the Remote Secure Element is
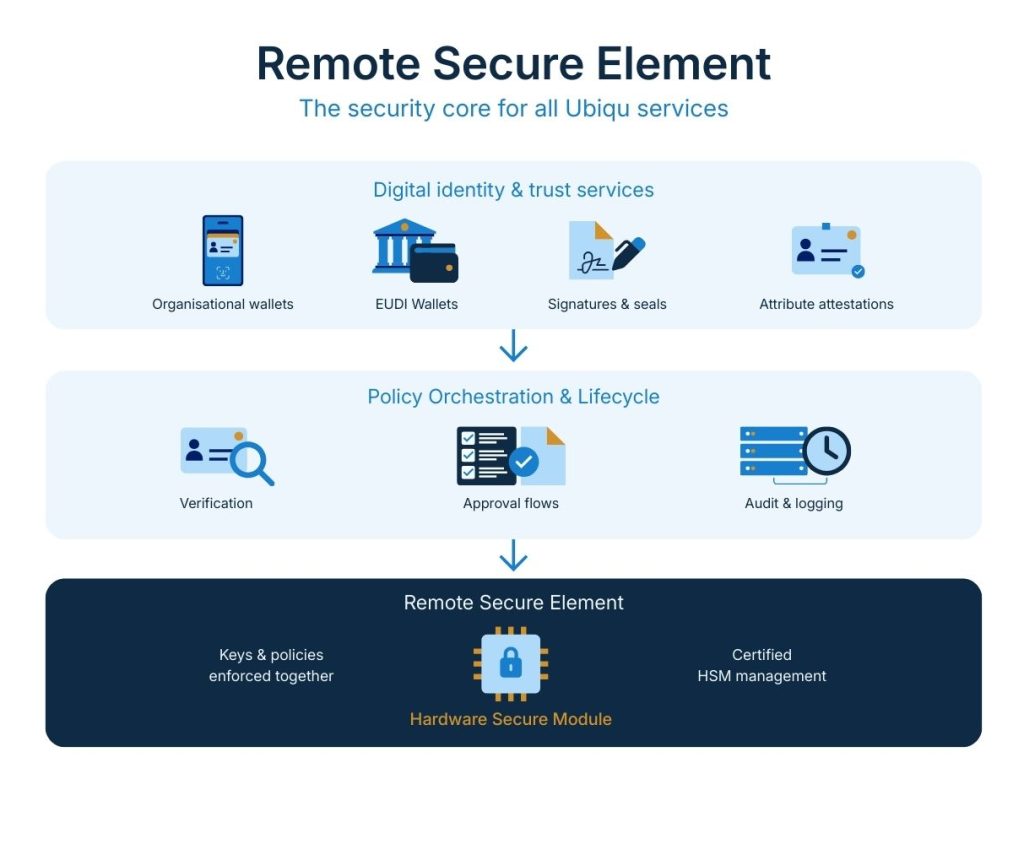
The Remote Secure Element is the secure core that wallets and trust services use to create qualified signatures and protect digital identities in wallets. It is built around a Hardware Security Module, widely regarded as one of the most secure ways to protect sensitive cryptographic material. By concentrating the most critical security functions in this one protected, certified environment, it reduces architectural complexity, lowers operational costs, and limits the components that need to be secured and audited.
The Remote Secure Element is a policy enforcement runtime implemented as code inside certified Hardware Security Modules (HSMs). It combines cryptographic key custody with policy evaluation, so that decisions about key usage are enforced within the same secure boundary as the keys themselves. External systems handle orchestration and lifecycle management, while the RSE ensures that signing, sealing, and authentication operations only occur when all policy conditions are met.
Operationalising the Remote Secure Element
The Remote Secure Element acts as a security foundation that can be applied where high-assurance identity, access, or trust services are required.
